
An LLM-powered assistant that helps product owners interpret, validate, and communicate IM8 security requirements within their system domain, ensuring faster, compliant deployments by bridging gaps with developers and vendors.
Compliance policy is not easy to comprehend. On one hand, policy makers have troubles wording the policy to be too specific. On the other hand, developers have troubles understanding how the policy comes into play for their products.
The side effect of the above problem is that decision making for policy compliance can also be inconsistent. As each person interpret to his own context. For the same System, Party A says comply. Party B says non-compliant. This defeats the purpose of compliance policy which is to provide a consistent governance for all.
For the purpose of this hackathon, we would scope compliance down to IM8 security compliance.
How might we help product owners translate IM8 security requirements into actionable tasks for developers, ensuring compliance and faster SaaS/app deployment?
After analyzing the key challenges product owners face in meeting IM8 security requirements during app service and SaaS deployments and through discussions with stakeholders, we identified that product owners often struggle to interpret IM8 within their system domain context, leading to miscommunication with developers and vendors. This misalignment results in delays, rework, and compliance risks. Existing compliance frameworks and tools provide guidelines but lack contextual adaptability, leaving product owners uncertain about what to ask and how to validate security requirements effectively. To address this, we explored the potential of LLM/GenAI to serve as a CSG-equivalent assistant, helping product owners translate security requirements in a structured, actionable way. By leveraging AI-driven insights, product owners can confidently assess IM8 applicability, ask the right questions, and communicate clear expectations to developers and vendors, ensuring faster, secure, and compliant deployments.
To define the problem accurately, we first identified the key stakeholders involved—product owners, developers, security teams, and vendors—and examined their pain points. Product owners often struggle with interpreting IM8 security requirements within their system domain, leading to unclear or incomplete guidance for developers and vendors. This misalignment results in miscommunication, compliance gaps, and deployment delays. Developers and vendors, on the other hand, lack a clear understanding of what is expected from them, making it difficult to implement security requirements correctly on the first attempt.
Next, we outlined critical questions to refine the problem scope. We asked: How do product owners currently translate IM8 requirements? Where do misinterpretations commonly occur? What are the bottlenecks in communicating security expectations? These questions helped us pinpoint gaps in existing processes and tools. We also evaluated available compliance frameworks and found that while they provide structured guidelines, they lack automation and contextual adaptability, leaving product owners uncertain about what to ask and how to validate security requirements effectively.
With these insights, we framed the core problem statement: How can an AI-powered assistant help product owners accurately interpret, validate, and communicate IM8 security requirements to developers and vendors, ensuring faster and compliant deployments? This problem statement encapsulates the need for an intelligent, context-aware solution that bridges the knowledge gap and streamlines compliance processes. Finally, we validated this problem statement with key stakeholders to ensure alignment with real-world challenges and deployment needs.
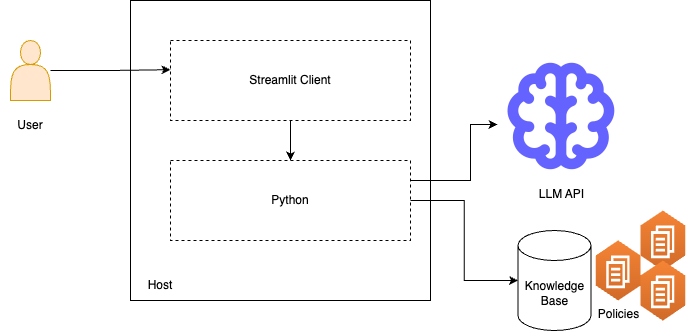
Our current tech stack is built around a Streamlit app in Python, enabling users to submit queries about system compliance or a specific SaaS. The backend connects to a knowledge base of policy documents, retrieving relevant information for analysis. Once the relevant documents are identified, the system prompts an LLM over an API with the user’s query, ensuring responses are contextually accurate and policy-aligned. The client then returns a chat-based response, potentially accompanied by a compliance score report, giving users a clear and actionable assessment of their compliance status. This architecture ensures efficient document retrieval, intelligent query processing, and real-time compliance insights in a user-friendly interface.
User Submits a Query
Knowledge Base Retrieval
LLM Query Processing
Response Generation
User Receives Compliance Insights
This streamlined workflow ensures efficient compliance verification, clear policy interpretation, and actionable insights for product owners and teams.
Accelerated Compliance Understanding
Improved Communication and Alignment
Faster and More Secure Deployments
Reduced Compliance Risks
Scalability and Consistency
Time Savings
Higher Compliance Accuracy
Increased Deployment Success Rate
Enhanced Decision-Making
Greater Adoption of Secure Development Practices
By leveraging LLM-powered automation, this solution not only streamlines compliance workflows but also empowers product owners and developers to achieve secure and efficient SaaS deployments with confidence.
As we approach the end of the hackathon, the team thought that the project could evolve from a query-based assistant to a comprehensive compliance intelligence platform, enhancing security and efficiency in SaaS and app service deployments.
Here are some possible steps we could take: