
A turn-based card game where players simultaneously act as both Attackers and Defenders, identifying vulnerabilities, launching cyberattacks, and protecting their systems in a strategic test of threat modeling skills.
A turn-based card game where players simultaneously act as both Attackers and Defenders, identifying vulnerabilities, launching cyberattacks, and protecting their systems in a strategic test of threat modeling skills.
How might we ensure that threat modelling workshop participants fully engage in the activity, retain key insights, and effectively apply these learnings in their future work?
CSG is currently developing a Threat Modelling Workshop to empower ICT professionals, enabling them to conduct cyber risk assessments more effectively and confidently. However, traditional approaches to understanding threat modelling and mitigation strategies are often perceived as dry and unengaging, which significantly hampers participant retention and comprehension. To maximize the workshop’s effectiveness, it is essential to integrate interactive elements that foster deeper understanding and long-term knowledge retention.
Challenges Identified:
Lower Engagement and Missed Knowledge Retention: Without the interactive game component, participant engagement is likely to decline, leading to reduced focus and passive involvement. Additionally, the previous quiz, which aimed to assess knowledge, was often avoided, with participants either hoping not to be called on or deliberately skipping it. This resulted in missed opportunities to reinforce learning and assess outcomes effectively.
Poor Decision-Making: A weak grasp of threat modelling concepts can hinder ICT professionals from effectively applying risk assessment techniques in real-world scenarios. This may lead to flawed analyses and suboptimal decisions when designing mitigation strategies.
Increased Vulnerability and Cybersecurity Costs: If team members lack practical knowledge in identifying and addressing threats, the organization faces heightened security risks. This knowledge gap can lead to misallocated resources, including unnecessary expenditures on ineffective mitigation strategies, increased manpower requirements, and overall higher cybersecurity costs.
We believe that gamifying the threat modeling learning experience will increase participant engagement in workshops and enhance knowledge retention, as research shows that gamification increases motivation and engagement by providing immediate feedback and fostering a sense of achievement. Additionally, studies have demonstrated that active participation in simulations or games improves retention, as it encourages learners to apply concepts in real-time scenarios, reinforcing their understanding and long-term recall.
Ref:
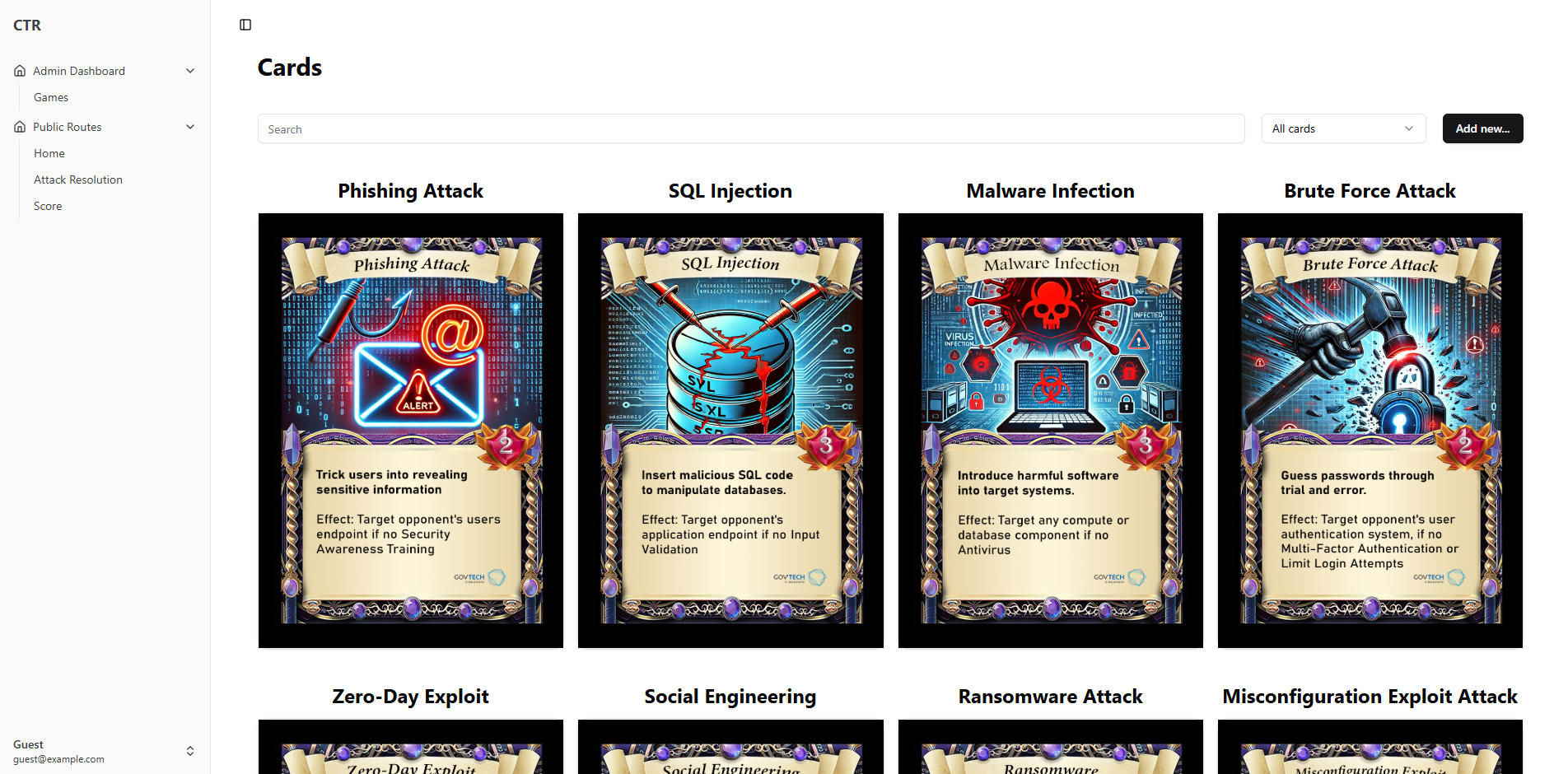
Capture the Risk is a strategic, turn-based card game where players simultaneously take on the roles of both Attacker and Defender to test their threat modeling skills. Players identify vulnerabilities, launch cyberattacks, and defend their systems in a dynamic battle of strategy and cybersecurity expertise. The game is designed to reinforce threat modeling concepts through hands-on, interactive gameplay.
Additionally, the team has developed a digital dashboard for game masters to efficiently track player progress and scores. This dashboard also includes features that allow game masters to manage game mechanics, such as determining attack resolution outcomes, ensuring a smooth and adaptable gameplay experience.
Key Features & Benefits:
Enhanced Engagement & Motivation – Gamifying the learning experience transforms traditional threat modeling learning into an interactive and immersive activity. By incorporating competition and strategy, the game keeps participants actively involved, making learning more enjoyable and reducing the likelihood of disengagement.
Improved Knowledge Retention – Research shows that active participation significantly enhances memory retention. By applying threat modeling concepts in real-time scenarios, players reinforce their understanding, making it easier to recall and apply these skills in real-world cybersecurity situations.
Hands-on Application of Threat Modeling – Instead of passively learning through lectures or theoretical exercises, players actively engage in identifying vulnerabilities, launching cyberattacks, and defending systems. This hands-on approach bridges the gap between theory and practice, ensuring participants gain practical experience in threat assessment and mitigation.
Fosters Critical Thinking & Decision-Making – By taking on the roles of both Attacker and Defender, players are challenged to think strategically, analyze risks, and make informed decisions under pressure. This dual perspective deepens their understanding of cyber threats and strengthens their ability to assess and respond to security challenges effectively.
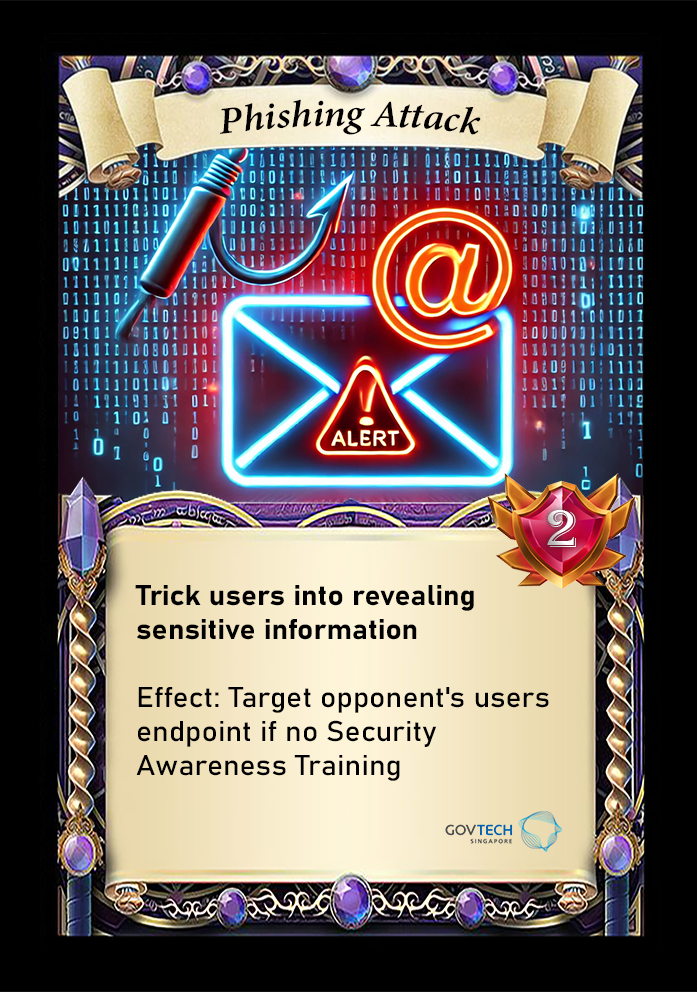
Version 1:

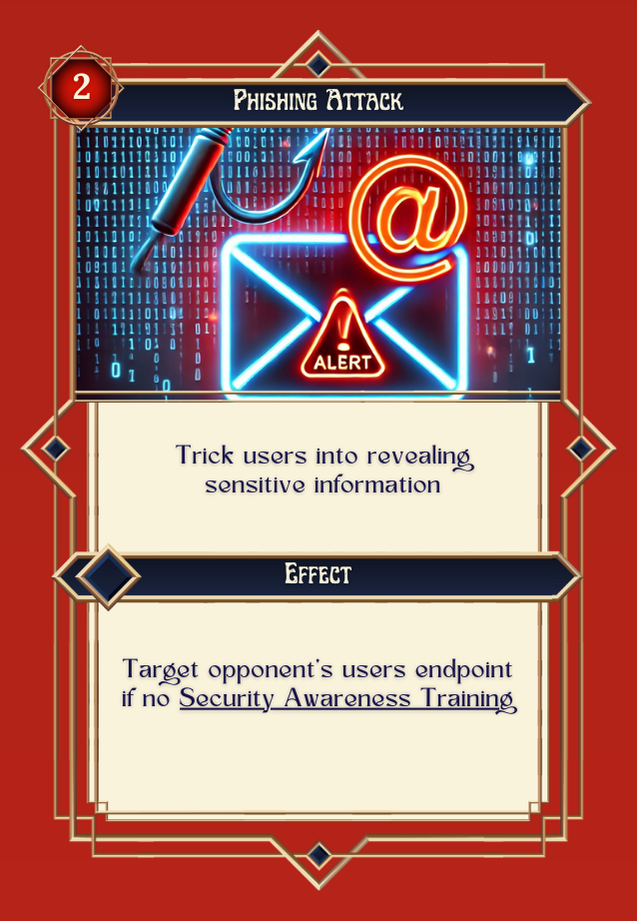
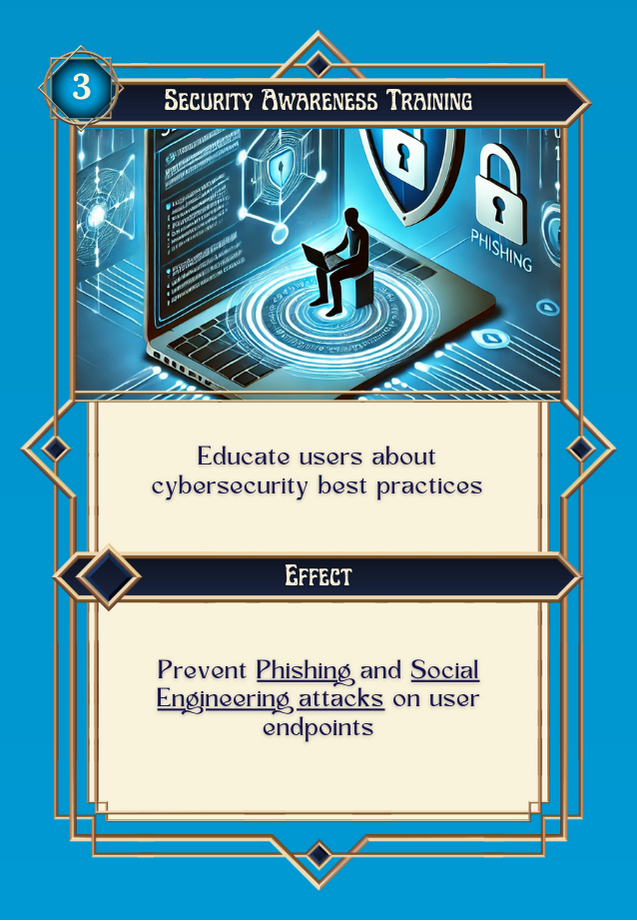
Version 2:
 .
. 